Creating a certificate signing request (csr) on windows
By eidias on (tags: certificate, categories: infrastructure)This bit will be useful for the next tfs build script modifications that I will describe in a later post.
Apparently there are a couple of ways to create a csr - openssl, online services, dedicated tools…
But there are also ways to create a csr without installing any software. There's the easy way (for those who have IIS installed) and the bit more complicated way (for those who like command line tools – that would be me)
First let’s focus on the easy way.
The following is a slightly modified version of instructions found on this site
- Press win+r and type in “inetmgr” – this will open the IIS manager that we all know and love
- Select your server on the tree on the left and from the “IIS” section displayed on the main panel select “Server Certificates”

- From the actions pane select “Create certificate request”
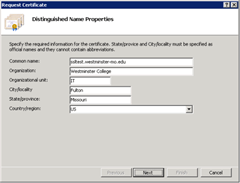
- Fill in all the details in the wizard and click next
- In the next screen, select the “Microsoft RSA SChannel Cryptographic Provider” and Bit Length of 2048 or higher. Click next
- Fill in the name for the csr and click finish
Voila – you’re done. Now you can send the csr to a CA for further processing.
Now let’s go for the bit more complicated way
We’ll be using the certreq command tool.
The best way to find out about how to use ‘one of these’ is the help command, so in your command line type in
1: certreq –?
You’ll get a list of available commands that you can further investigate. (I recommend the certreq –v –? option – gives you even more stuff to scroll the screen!)
Certreq needs a .inf file that stores data about the certificate you are requesting for, so let’s create that file. You can find all the available syntax and options here, but for now, lets focus on the basic stuff. Create a .inf file with the following content:
[NewRequest]
;CN - Common Name, OU - Organizational Unit, DC - Domain Component
Subject = "CN=...,OU=..,DC=.."
HashAlgorithm = sha1
KeyAlgorithm = RSA
KeyLength = 2048
RequestType = PKCS10 | PKCS7 | CMC | Cert
FriendlyName = "..."
and fill in the dots.
There are various options that can be provided. You can see a sample after executing certreq –new –?. If you do not supply an option, a default will be taken.
Just on the safe side, make sure you provide a KeyLength with value of at least 2048 (the default is 1024)
Now go to the directory you saved the .inf file in ad type:
1: certreq –new myCert.inf myCert.req
And that’s pretty much it.
Cheers

 back
back